Using microservices for building apps is rapidly gaining popularity as they can bring so many different benefits to the business: they are safe and reliable, scalable, optimize the development time and cost, and are simple to deploy.
In our previous articles, we discussed the best tools to manage microservices, the advantages and disadvantages of using microservices and the differences they have with monolith architecture, and hexagonal architecture.
Despite multiple benefits, app development with microservices has many challenges:
However, using the correct microservices design patterns can overcome the challenges mentioned above and even maximize performance. There are actually many benefits the patterns can bring to your business, but remember that design patterns are not "one-size-fits-all" solutions. Thus, pay attention to the advantages and disadvantages of each pattern and when to use them so that the implementation would be beneficial for your goals.
And now, let us provide you with our favorite microservices design patterns and things to pay attention to before implementation:
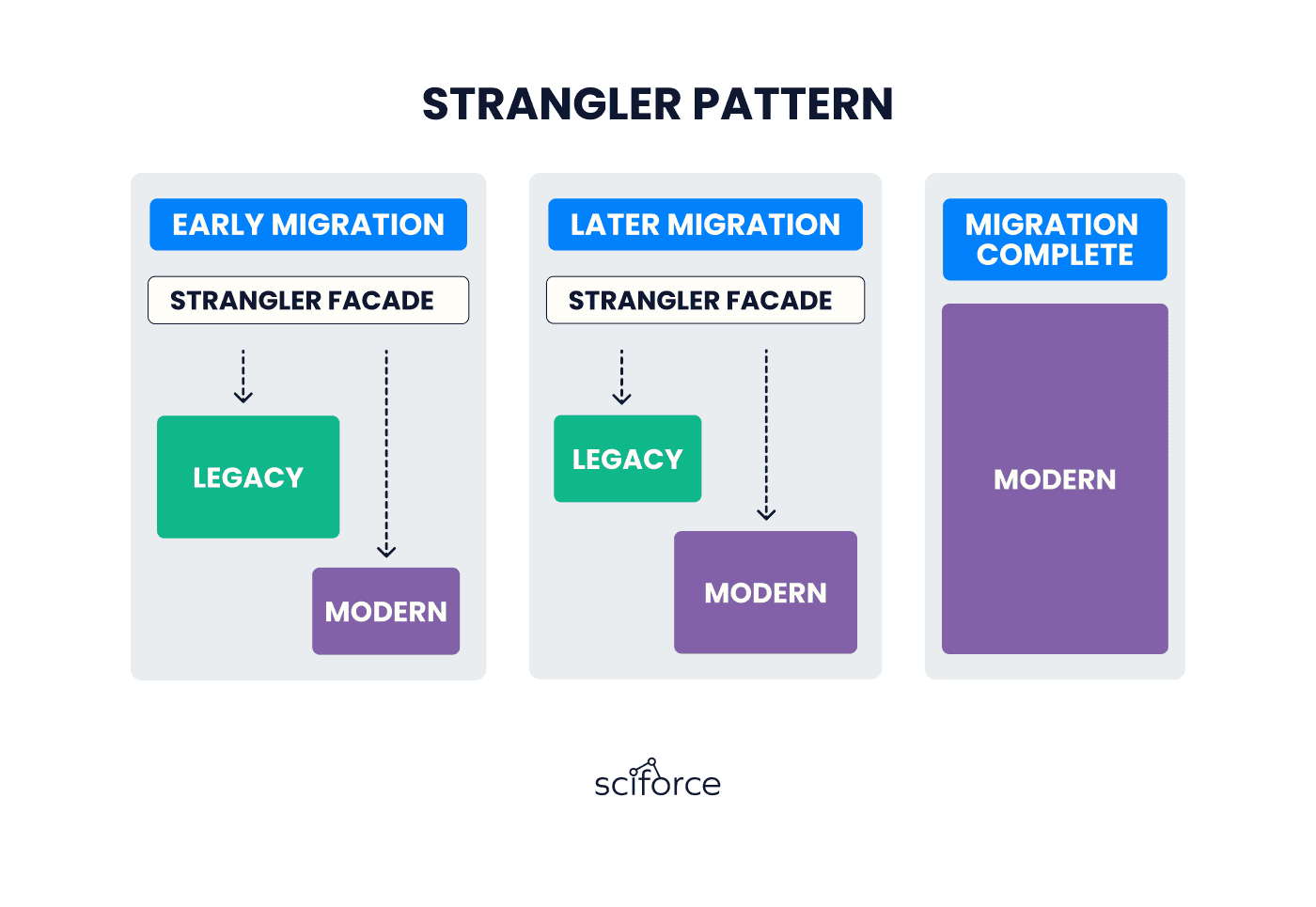
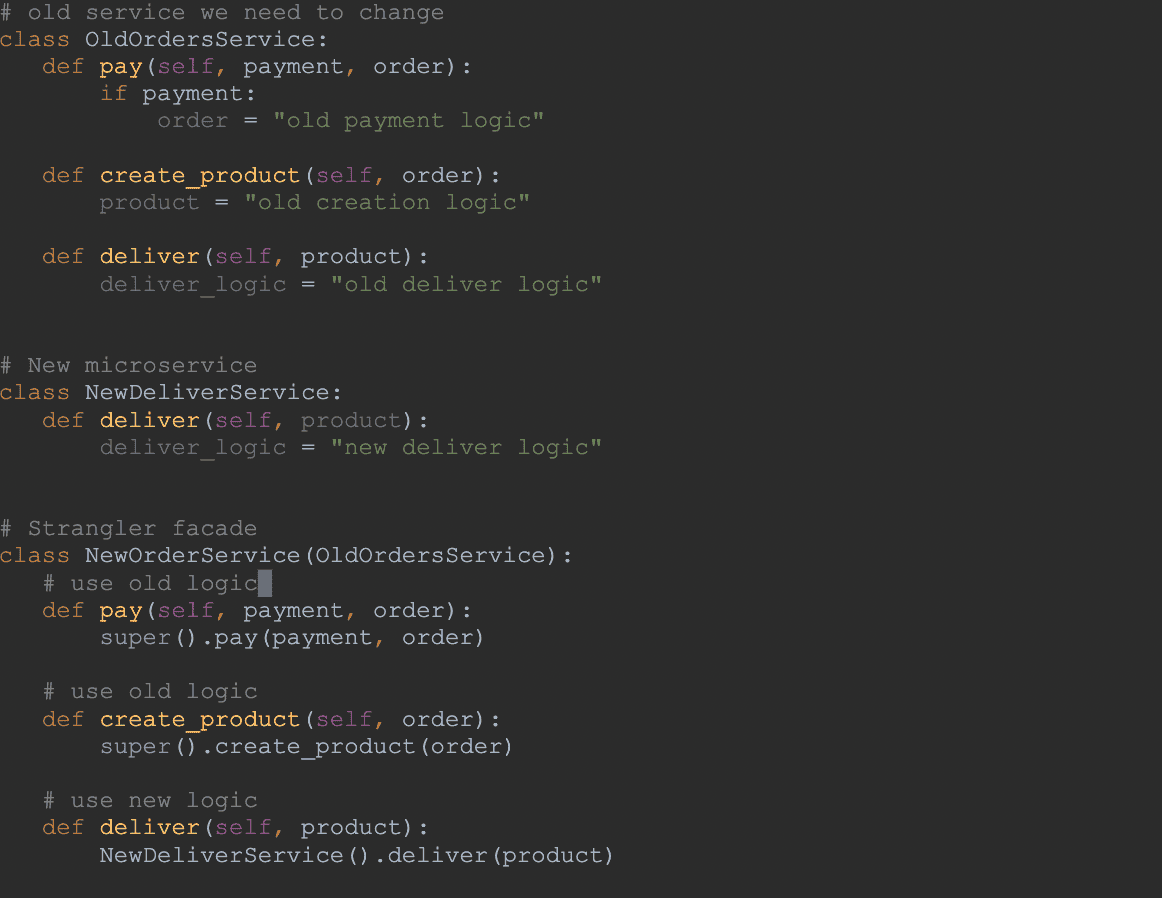
The strangler pattern can be an excellent solution if your goal is moving incremental existing Monolithic applications to Microservices. Such a procedure can be challenging as it may disrupt the application's availability, but using the Strangler pattern can minimize such risks.
Let us explain to you how it works: basically, it allows a Monolithic application to migrate to Microservice Architecture by gradually replacing specific functionality with new Microservices. After this, the new application system replaces all features from the previous system.
Now that we know how this pattern works, let's understand what the advantages and disadvantages of the Strangler pattern are.
Advantages:
Disadvantages:
When to use the Strangler pattern
When not to use
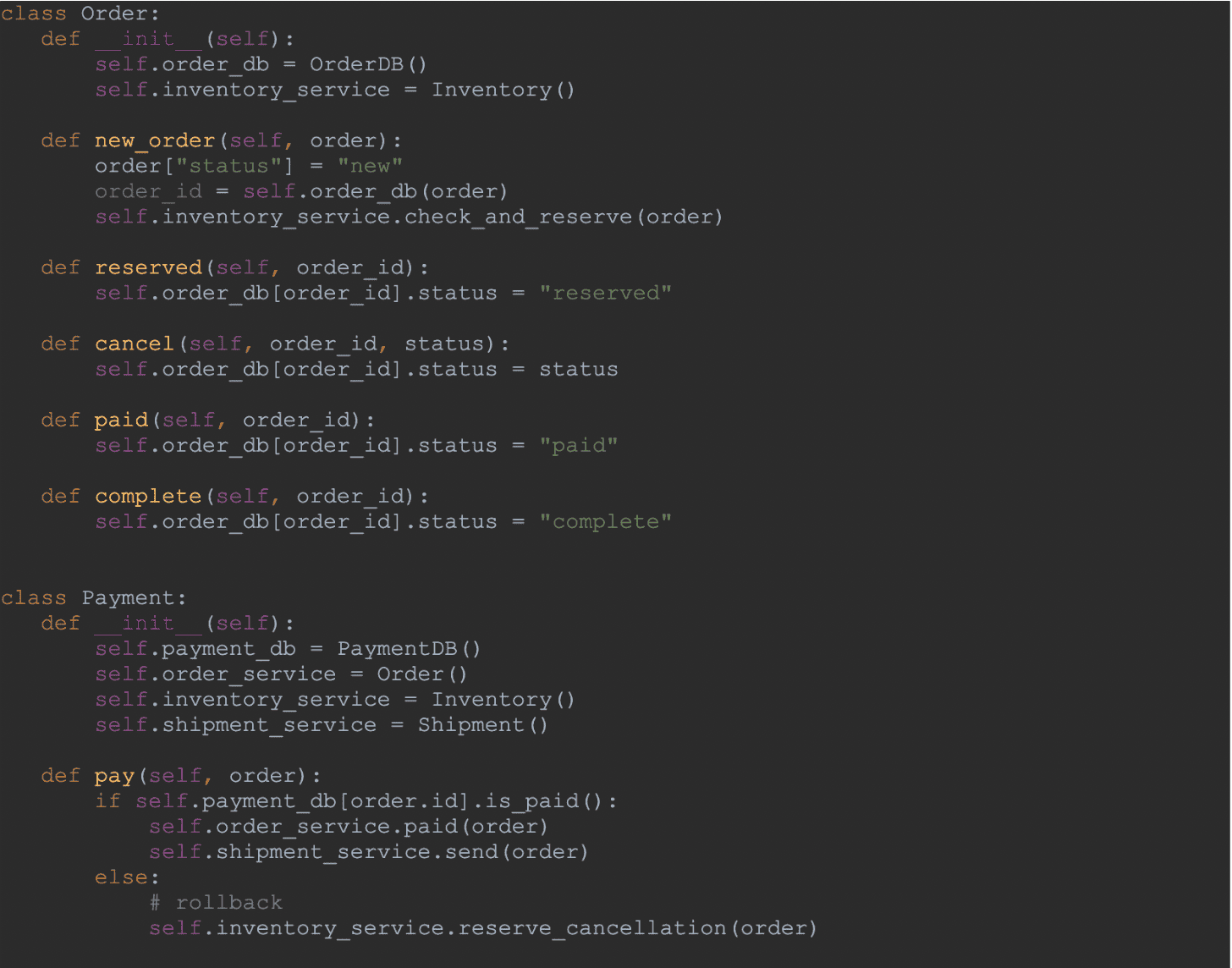
Saga pattern helps establish consistency in distributed applications and coordinates and manages transactions between multiple microservices to maintain data consistency. This pattern was developed in 1987 and is considered to be one of the oldest patterns, and was designed as a conceptual alternative for long-running database transactions in SQL databases. And now, in the modern context, this pattern is widely used for distributed transactions as well.
How does it work? Each transaction is followed by an event that triggers the next transaction step, and, in case the local transaction fails, Saga executes a rollback transaction compensating for the failure. Basically, to undo the preceding local transactions' changes.
You can see this process in the picture below.
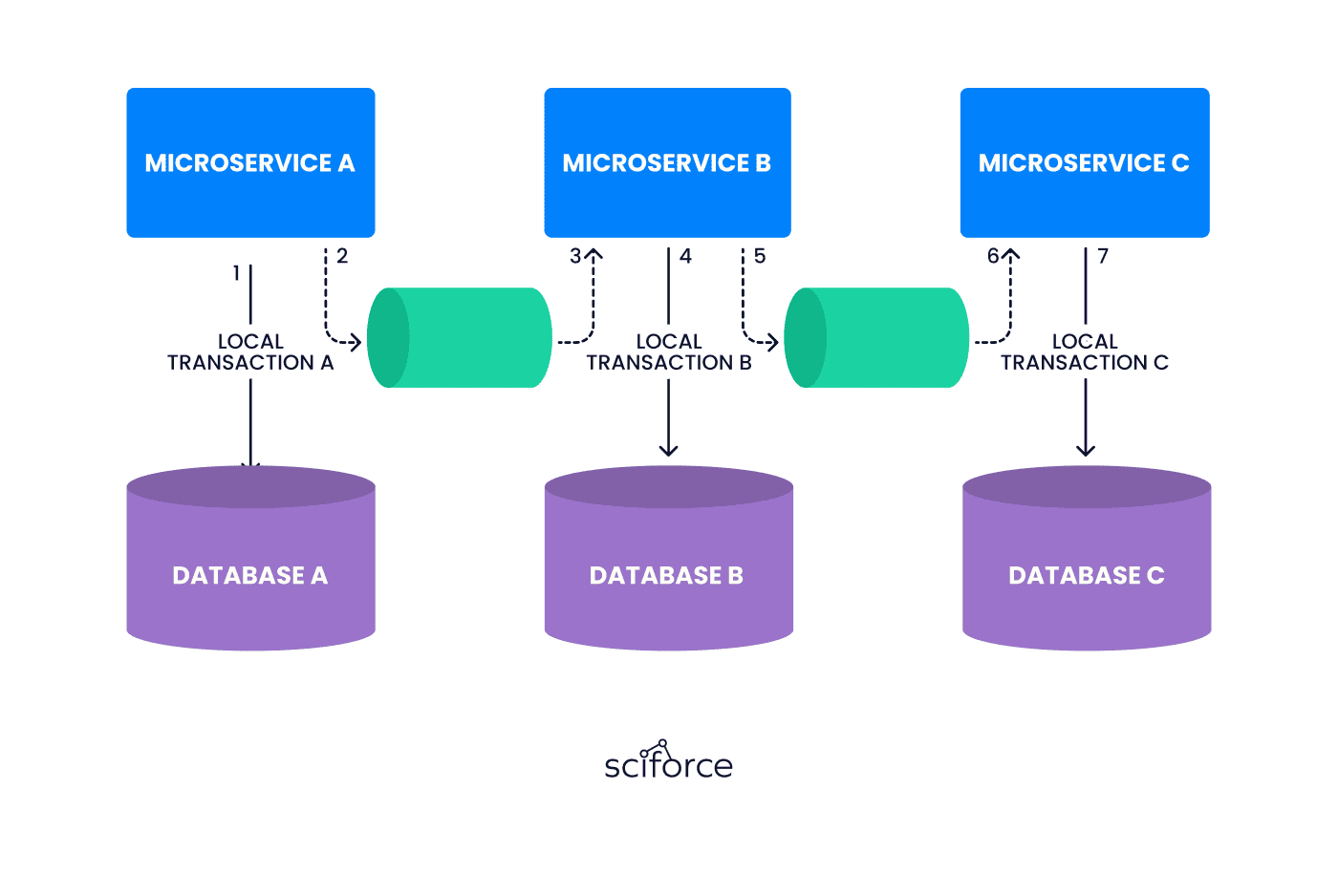
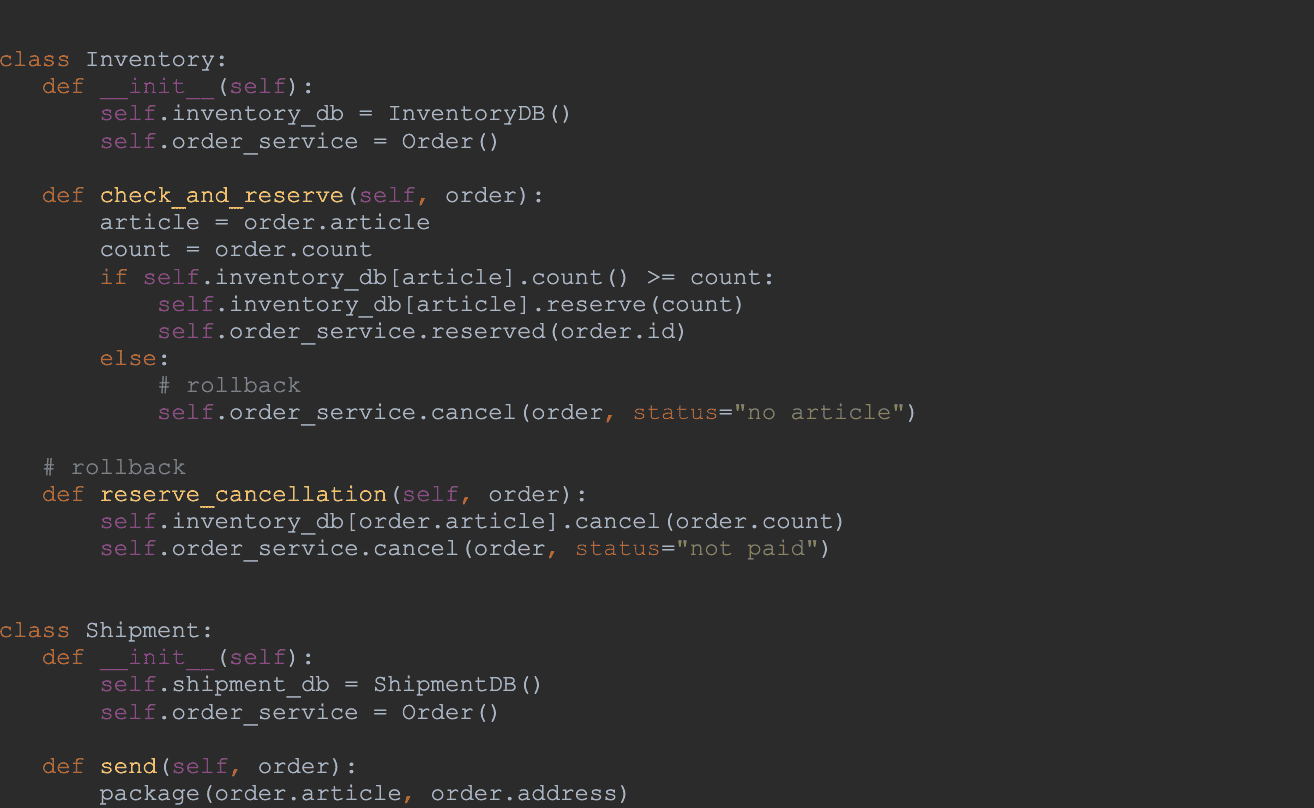
There are many ways to implement the SAGA algorithm, but these 2 are the most popular: Events/Choreography: here, the Microservices are responsible for the creation of new events after completing their local transaction. Decentralized co-ordinations where each Microservice produces and listens to other Microservice's events/messages and decides if an action should be taken or not.
Command / Orchestration: an orchestrator (arranger) manages all the transactions and directs services to execute local transactions. Basically, this orchestrator communicates with the other services and commands them what to do and when. Such communication takes place in a command mode.
Now, let's discuss the advantages and disadvantages of this pattern.
Advantages:
Disadvantages:
When to use the Saga pattern
When not to use Saga
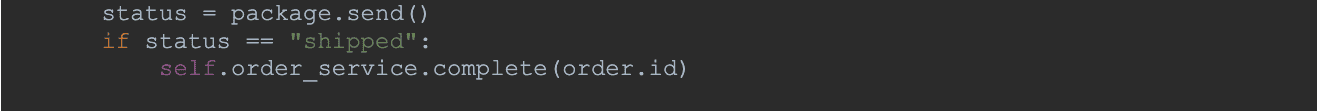
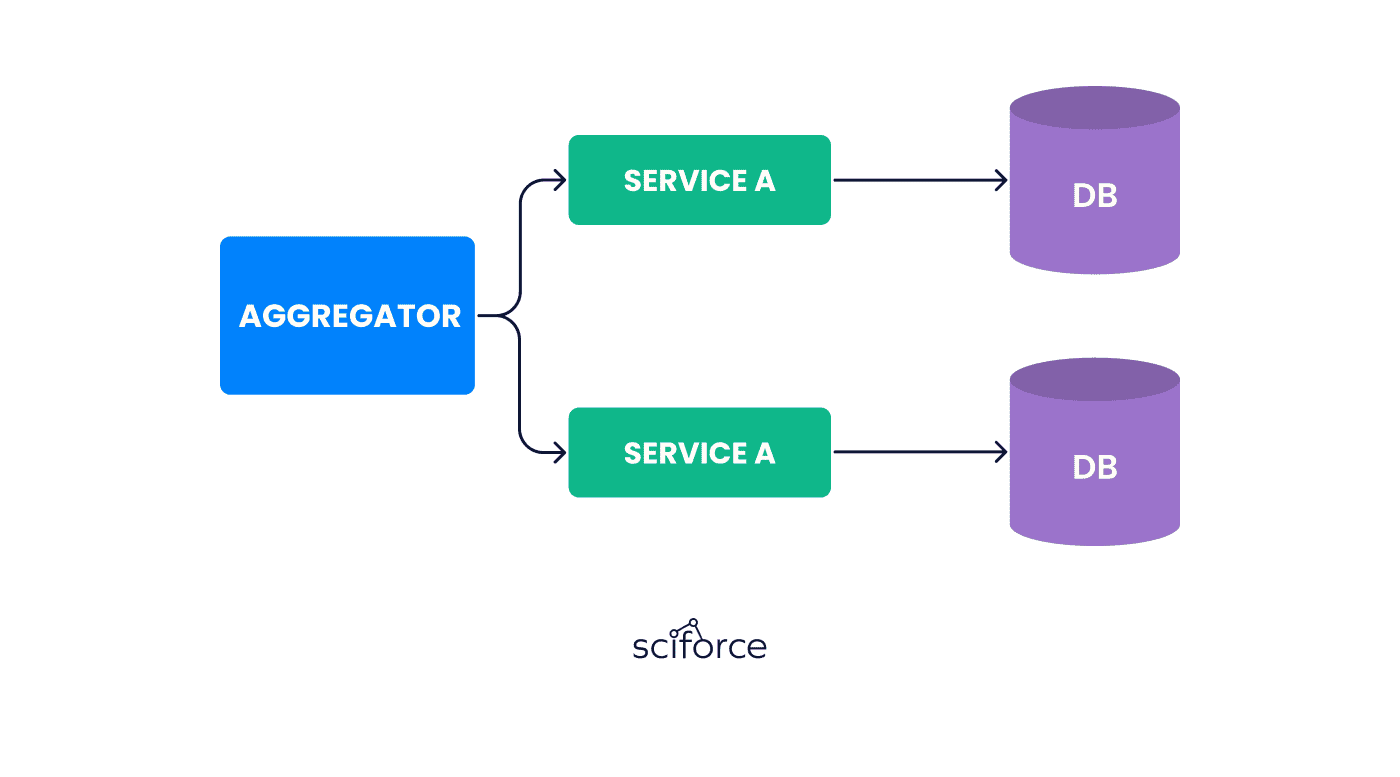
The Aggregator pattern is a service that receives a request from the client or API Gateways, and, after that, it makes requests of multiple services, and then, it combines the results and responds back to the initiating request in 1 response structure.
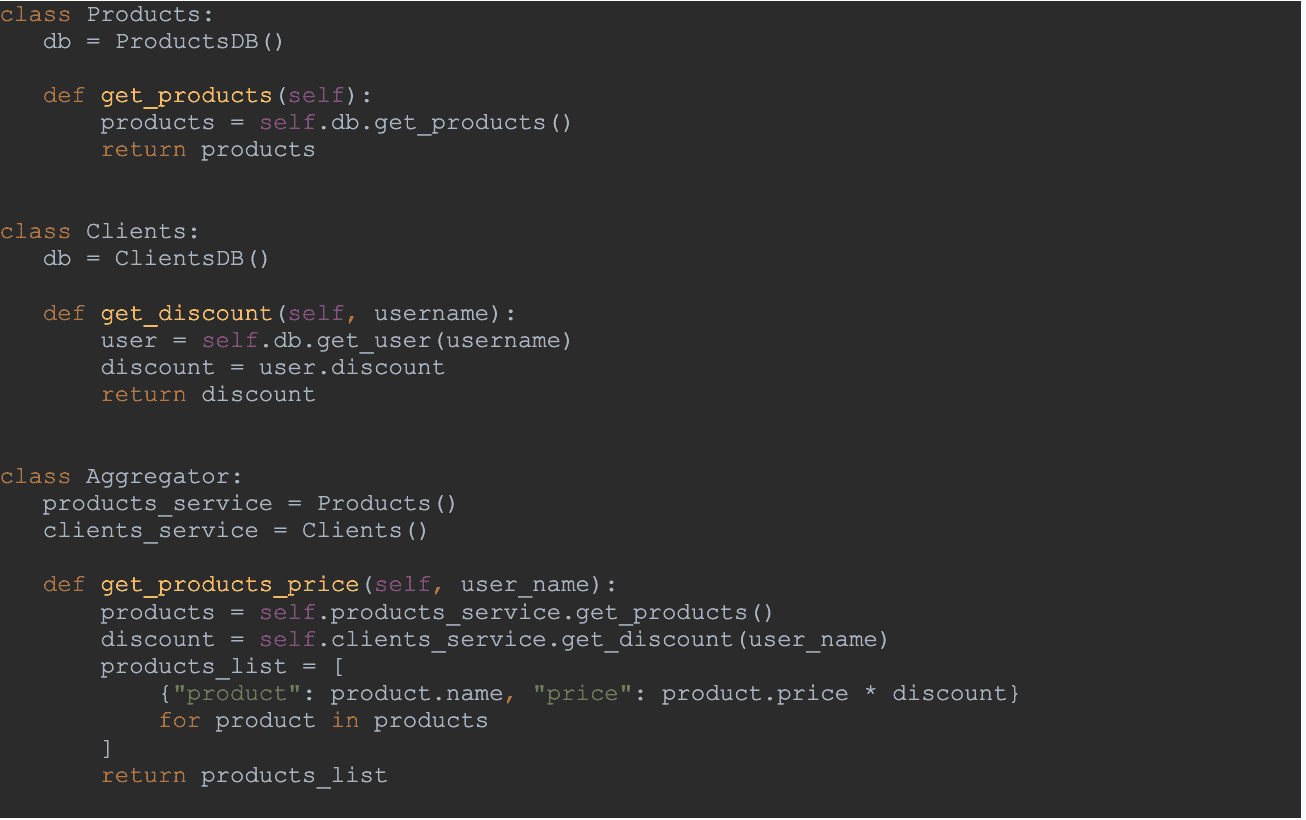
And for now, let's discuss the main advantages and disadvantages of the aggregator pattern.
Advantages:
Disadvantages:
When to use the Aggregator Pattern
When not to use the Aggregator Pattern
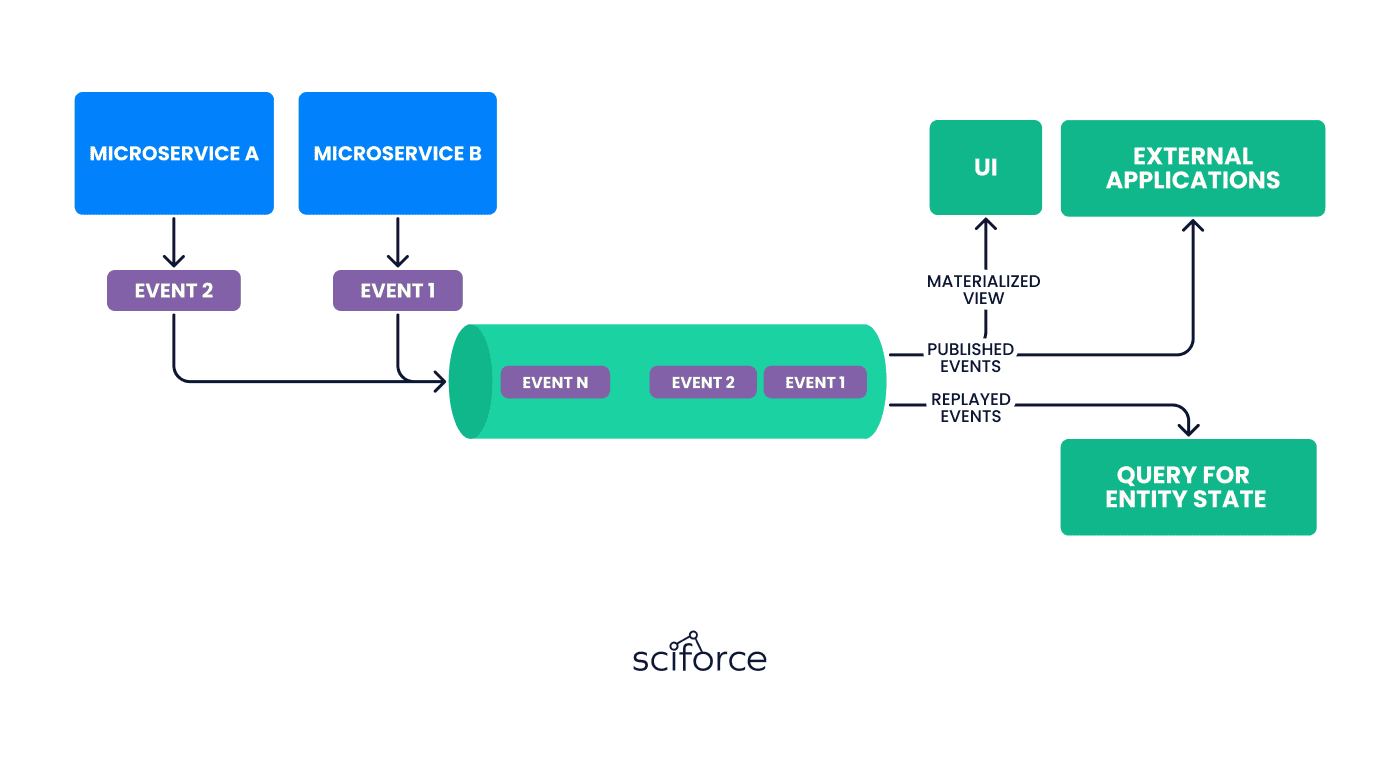
In practice, event sourcing requires careful management of the event store, which contains the history of all events in the system. This includes ensuring the durability and reliability of the event store, as well as managing the performance and scalability of the system as it grows.
Overall, event sourcing is a powerful pattern for building scalable, maintainable, and reliable microservices-based systems, but it requires a deep understanding of the underlying principles and practices to implement it effectively.
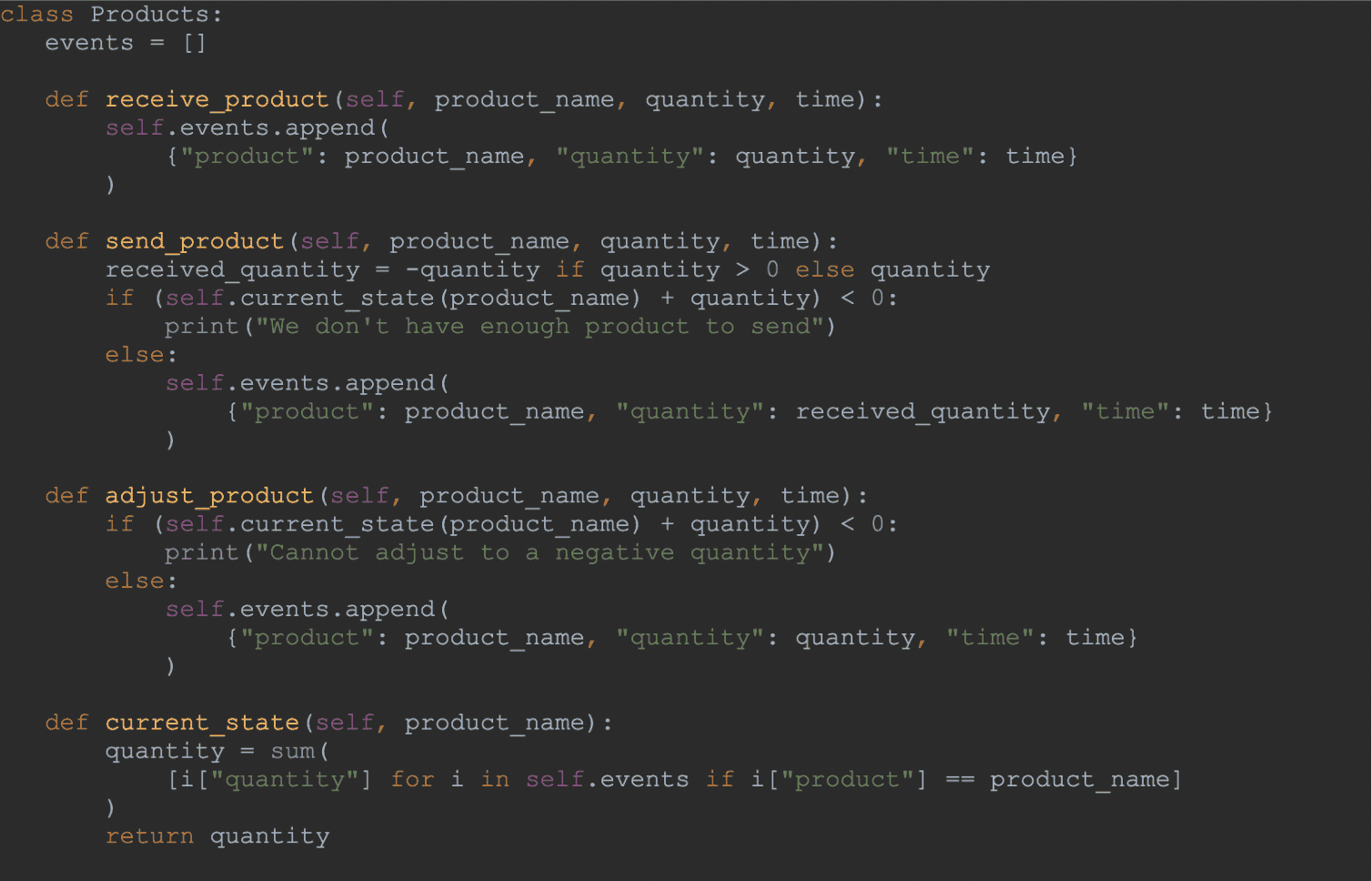
Let us provide you with the advantages and disadvantages of the Event sourcing pattern.
Advantages:
Disadvantages:
When to use Event Sourcing
When not to use Event Sourcing
CQRS, as a design pattern, basically treats retrieving data and changing data differently. Command Query Responsibility Segregation simplifies the query process and hides complex, multi-system changes by using command handlers. This design pattern was created to ensure that a method working with data is only allowed to perform one of two tasks: to retrieve the data or modify it. But it can not do both.
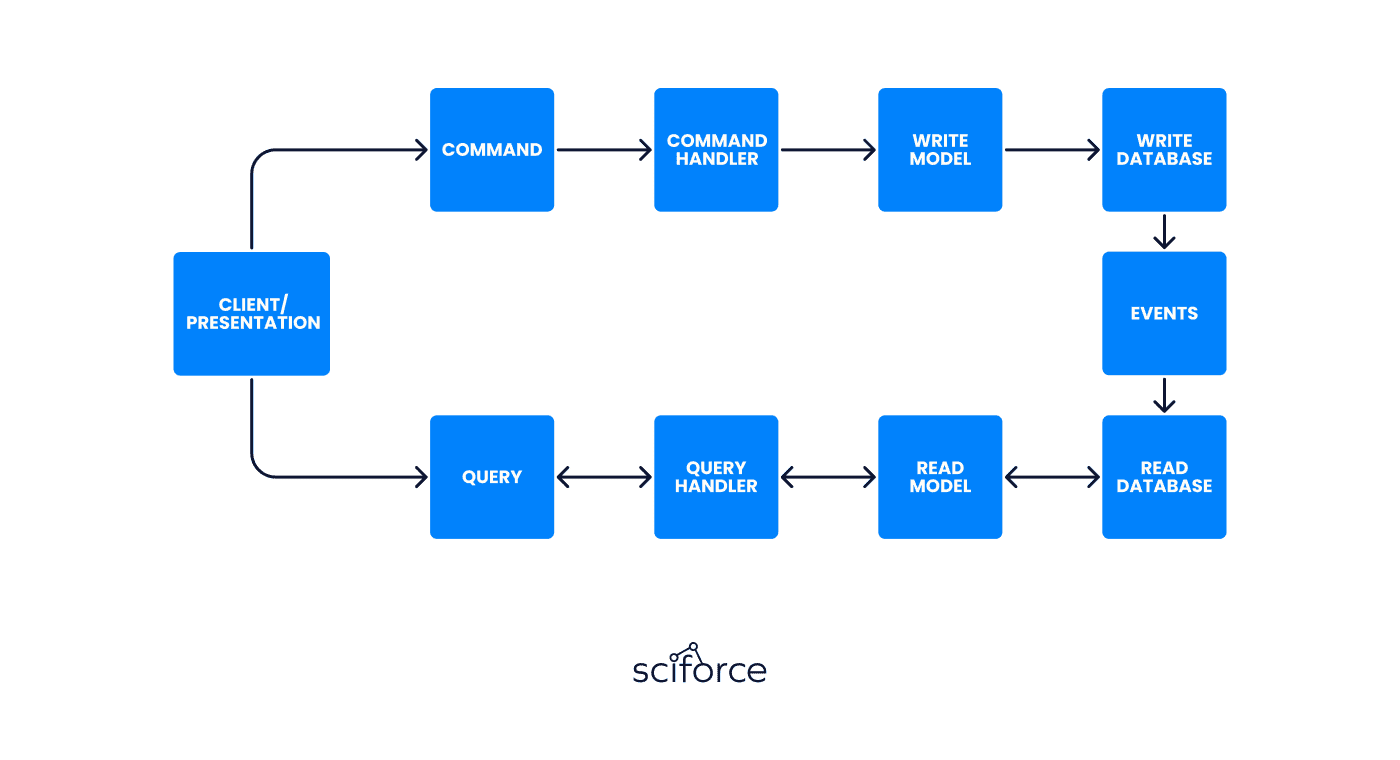
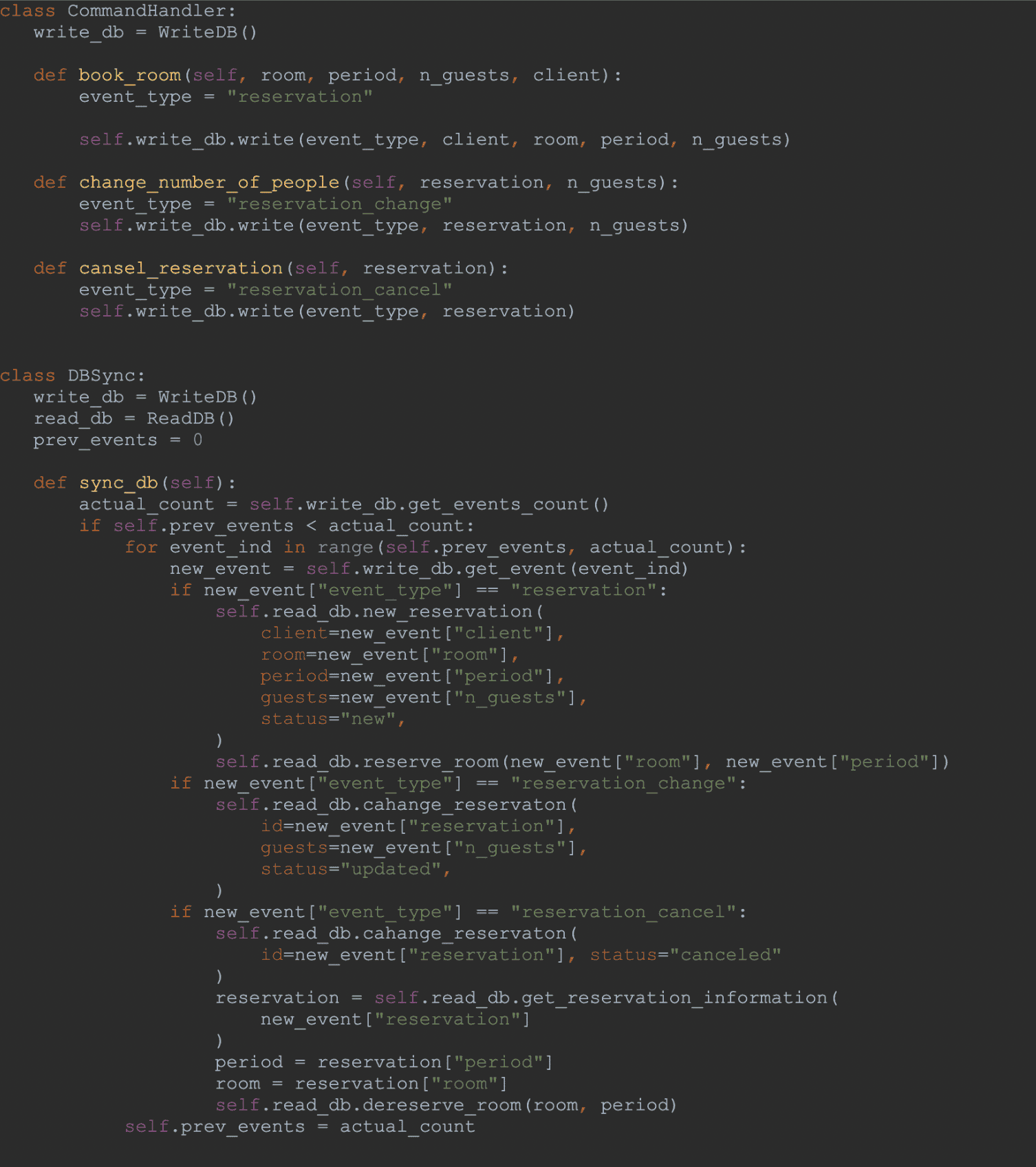
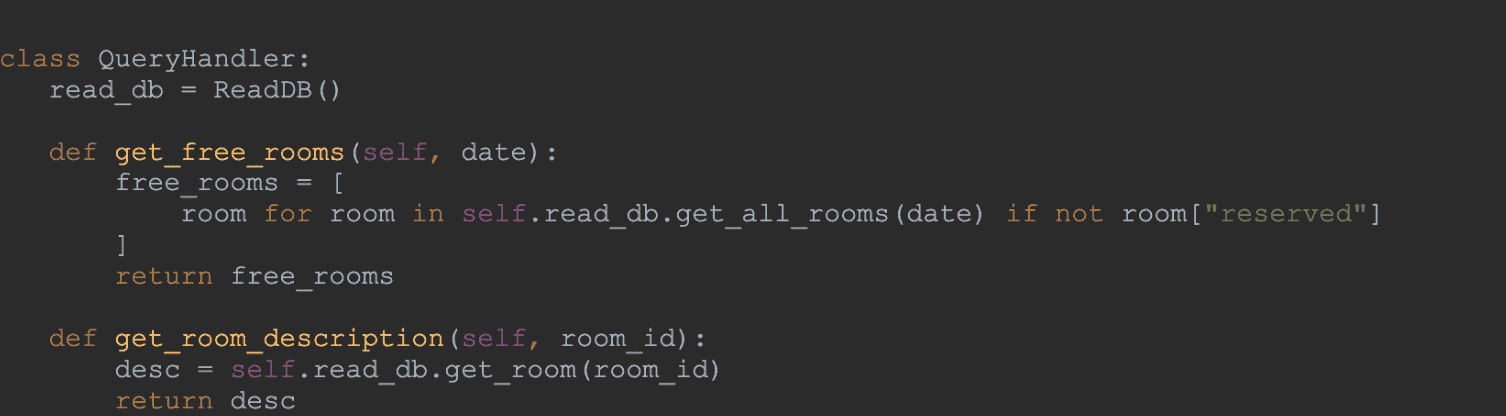
The advantages and disadvantages of this system are the following:
Advantages:
Disadvantages:
When to use CQRS
When not to use CQRS
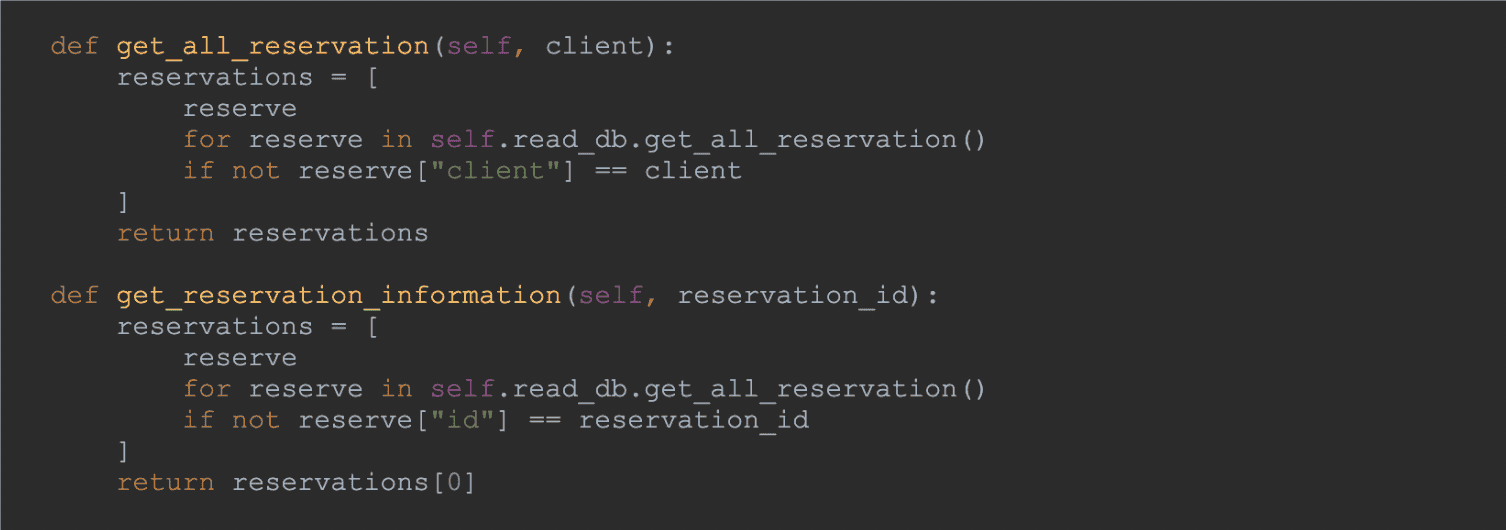
It is a well-known fact that usually, the Frontend and the Backend applications are decoupled and separate services, especially when we are talking about Microservice Architecture. The problems occur when there is a need to use the same backend Microservice for both the Web and the Mobile clients, as the requirements of those two systems are completely different.
, Backends for frontend patterns can become an excellent solution that could be used in scenarios where each UI gets a separate backend customized for the specific UI. Furthermore, it has multiple advantages.
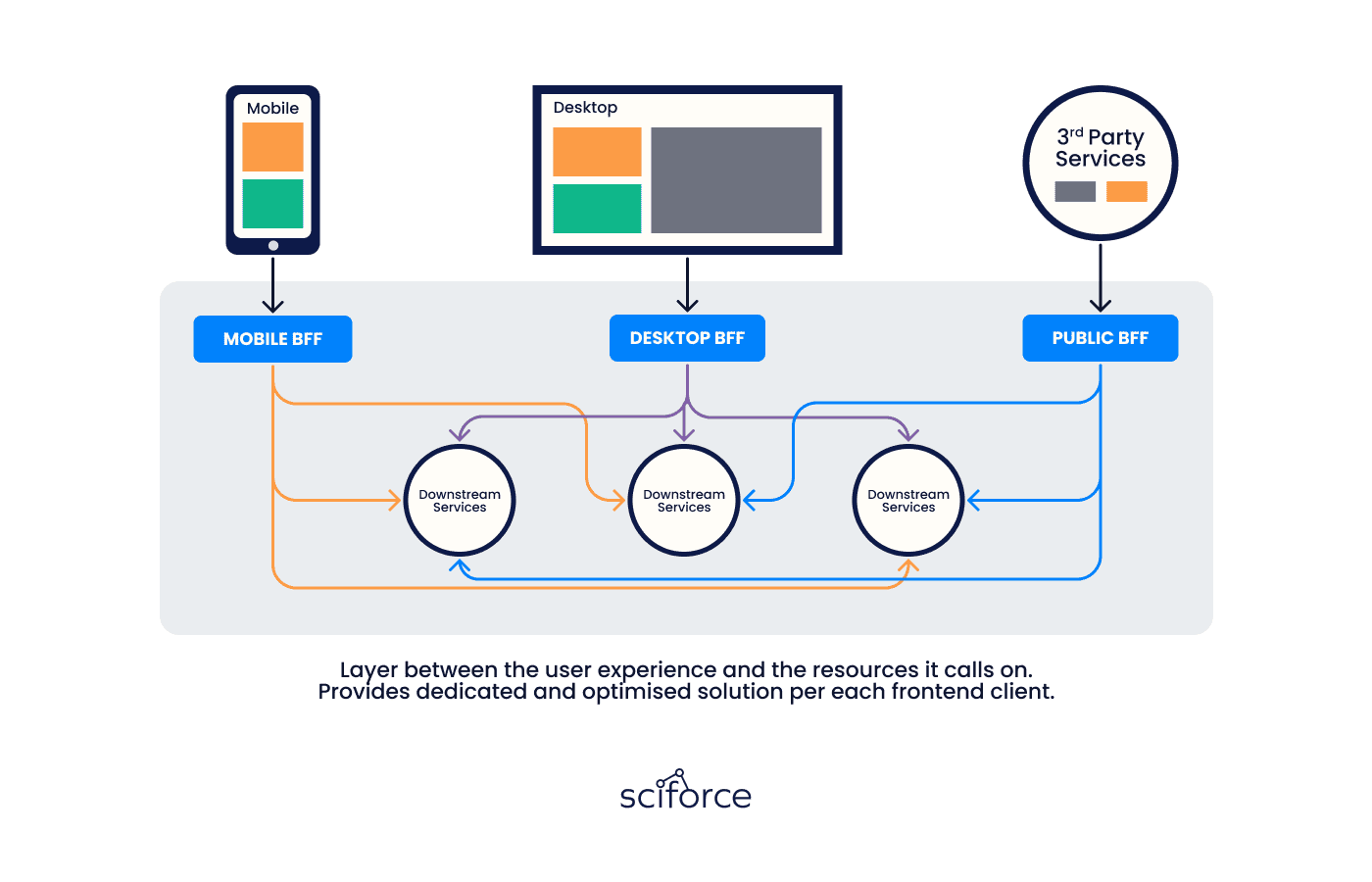
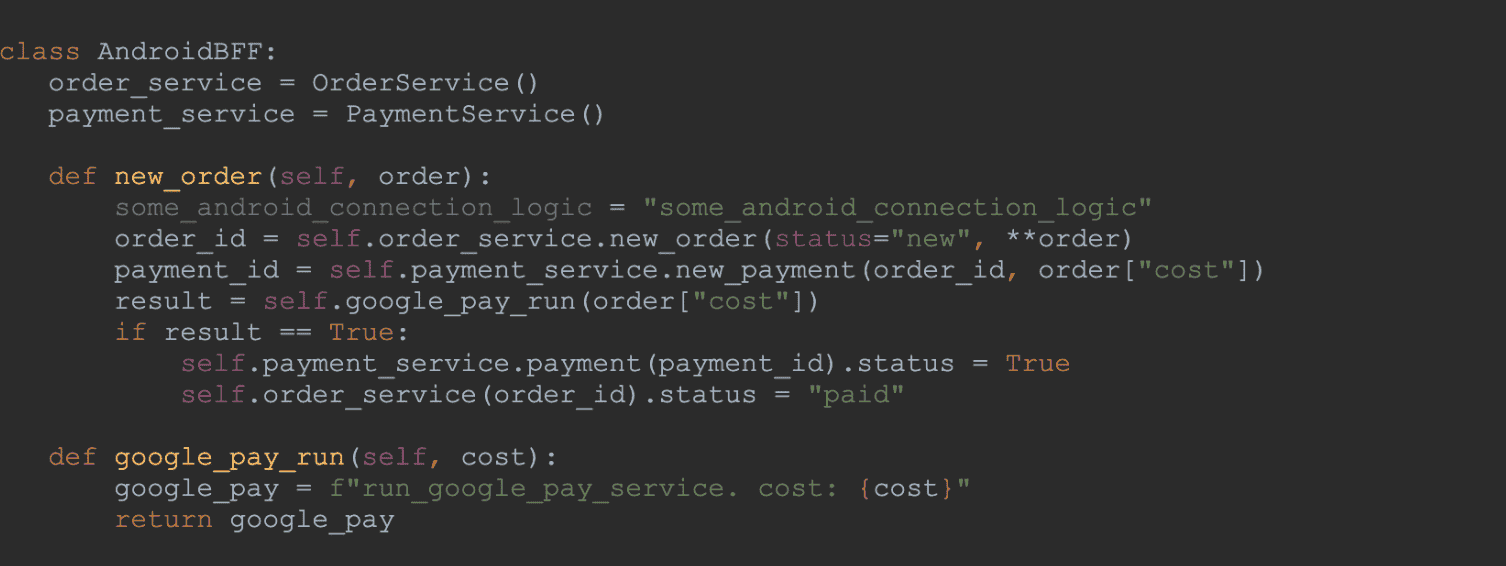
Let us provide you with the main advantages in more detail.
Disadvantages:
When to use Backends for Frontends
When not to use Backends for Frontends
In the modern software development process, Microservice Architecture can provide long-term benefits. But, keep in mind that Microservice Architecture can not be used in every use case. If such technology is implemented incorrectly or in the wrong system, Microservice Architecture can cause more problems than bring you benefits. Thus, it is better to delegate this complex process to professionals who will follow a set of best practices and find a custom solution for you.